SIGMA BLOG
Featured
There's a better way to do business intelligence, and it starts with Sigma.
Recent Posts
Thank you! Your submission has been received!
Oops! Something went wrong while submitting the form.
All
AI Apps
Product
Input Tables for Postgres: Build AI Apps with Data Writeback
Turn your Postgres database into operational apps. Sigma Input Tables let business teams write data directly to Postgres, building governed truth for AI.
All

AI Apps
Workflow Recap: Use the BUILD Framework to Design Better AI Apps in Sigma
Build better AI-powered workflow applications using the BUILD framework, with practical examples and best practices from Sigma’s Workflow 2026 session.
All

AI Apps
Workflow Recap: Accelerate the Close Process with AI-Assisted Variance Commentary
Build a smarter P&L workflow with an AI-powered financial statement generator that combines modeling, commentary, and variance analysis in one governed system.
All
Sigma News
AI Apps
Updates
What Happened at Workflow 2026: Insights from Sigma’s First User Conference
Explore the conference highlights: product announcements, hands-on training, and real-world examples of businesses building AI Apps and workflows in Sigma.
All
AI Apps
Embedded Analytics
Move Beyond Static Spreadsheet Analysis and Act on Insights in Real Time
Spreadsheets force static thinking in a dynamic world. See how Sigma helps you solve for your dynamic workflows with a spreadsheet experience.
All
Product
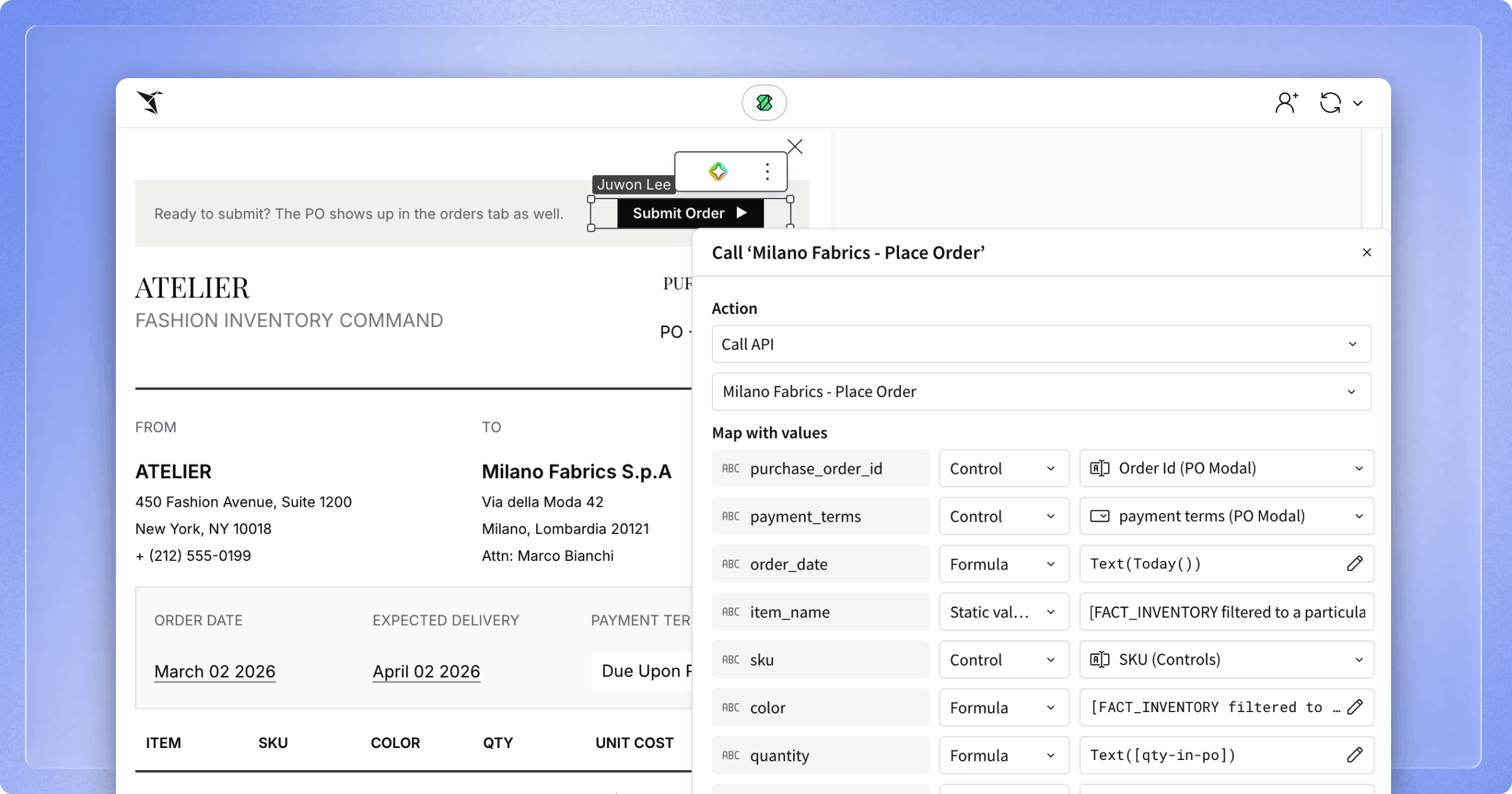
Introducing API Actions: Connect your AI Apps to External Systems
Expand the boundaries of what you can build in Sigma with API Actions, a seamless way to trigger API calls based on workbook and app activity.
All
AI Apps
Embedded Analytics
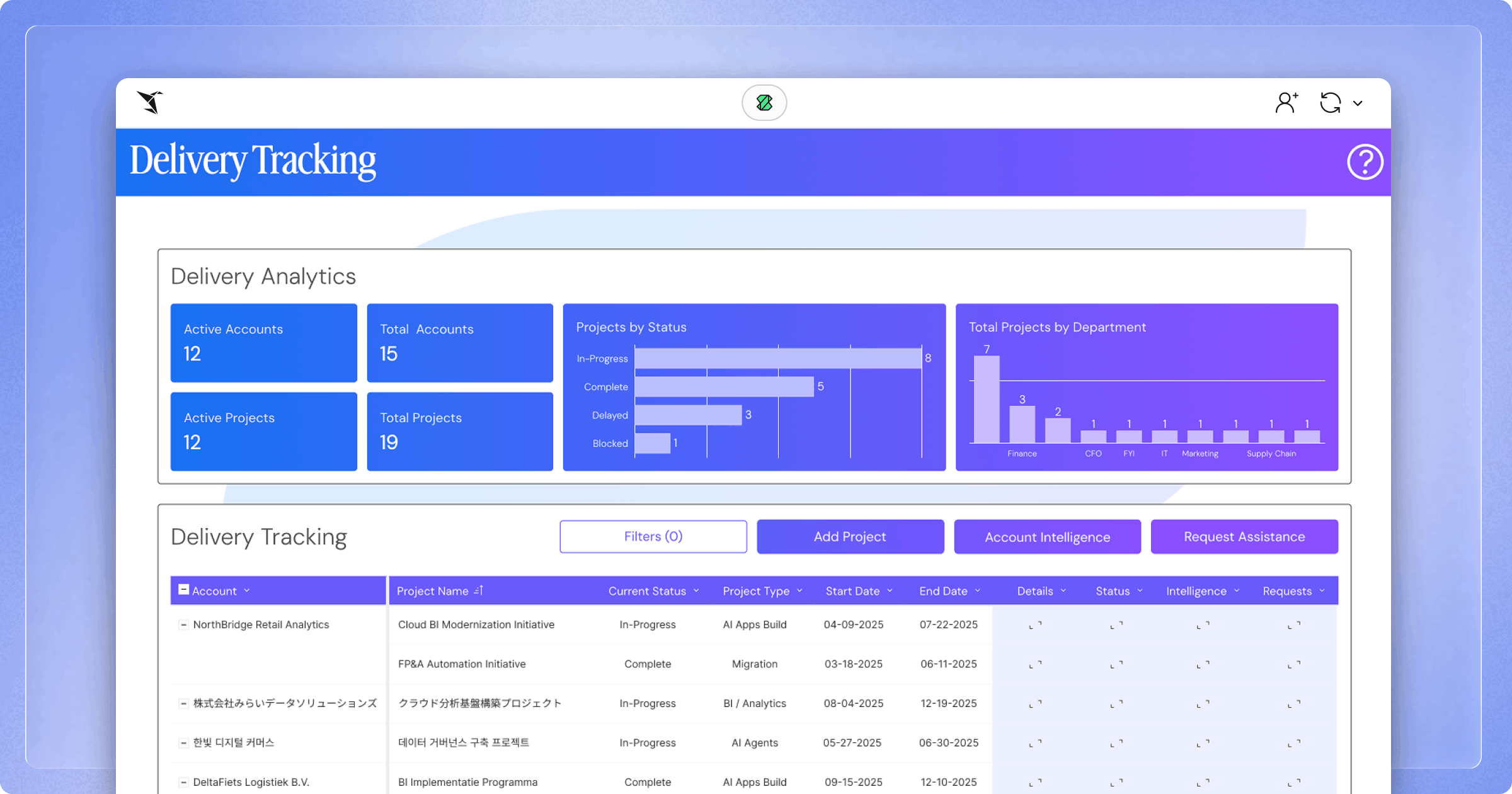
Build > Buy: How Sigma saved $500K building a Partner Portal on Sigma
Sigma built a warehouse-native Partner Portal using AI Apps, saving $500K and replacing five SaaS tools. Learn how writeback, embedded analytics, and secure data sharing power real-time GTM workflows.
All
Stay in the Loop
Subscribe to our newsletter for the latest insights on cloud analytics, product updates, and data strategy best practices.