
Have peace of mind with Sigma, like these companies




























Modular governance with RBAC and approvals ensures scalable change management and reusable data assets that streamline analysis and minimize redundancy.

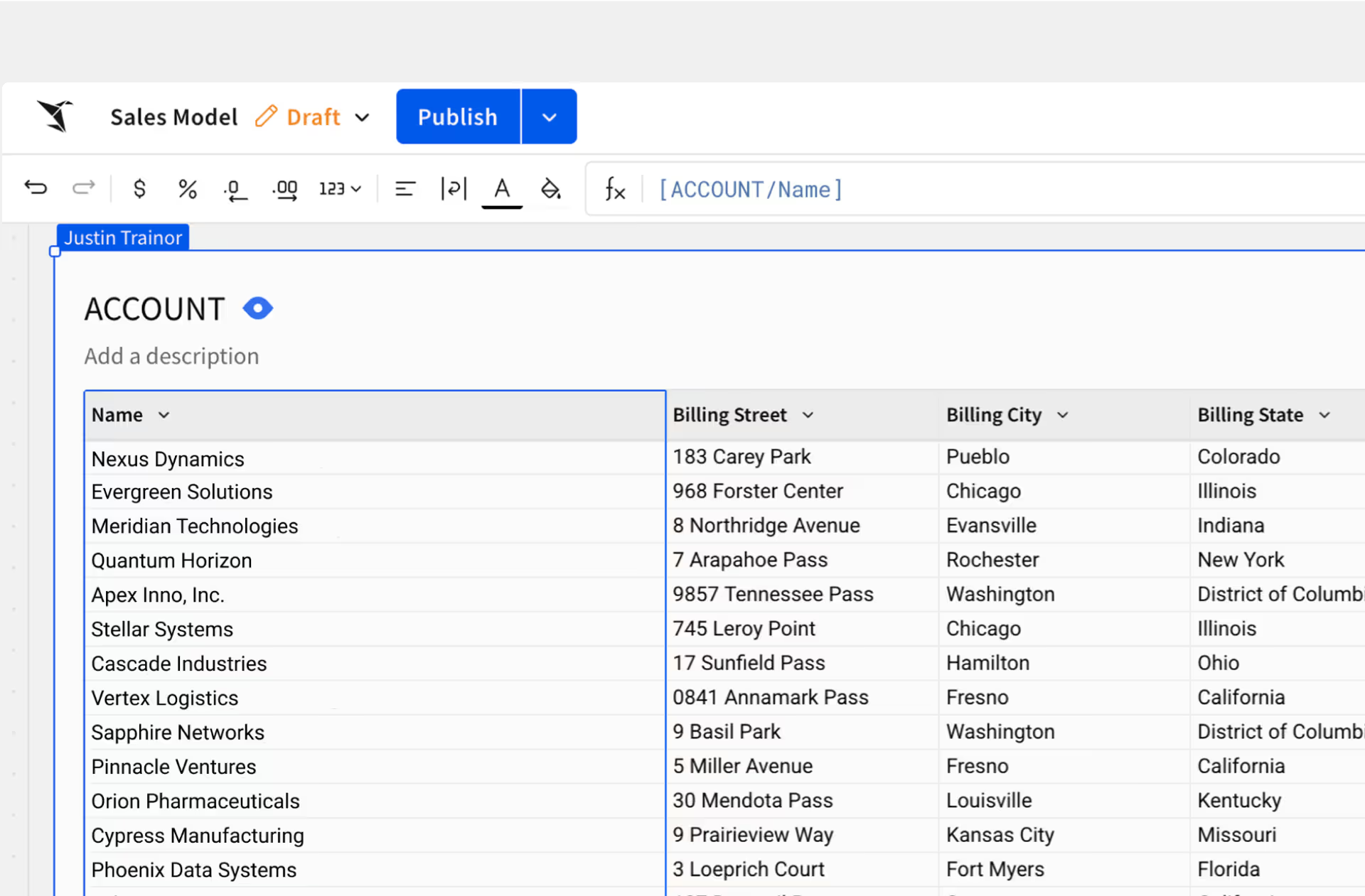
Flexible modeling that adapts with your use cases, allowing you to create models only when it’s useful—without forcing proprietary modeling languages on your data team.

Business users know business logic best—empower non-technical users to self-serve, model, and explore data in their own language with GUI-based tools, minimizing ad hoc requests.
Centrally define metrics and business logic for consistent, accurate insights across your data stack—using your data model or our semantic layer.

Ask Sigma indexes data models, metrics, and relationships to accurately answer questions—ensuring every response is grounded in your defined semantics for trusted results.

Meet with a Sigma expert today and learn how you can unlock consistent, governed metrics with Sigma’s semantic layer.
Dharmesh Patel
VP of Analytics and Business Operations, Druva

Top teams choose Sigma.
See for yourself. Sigma is a G2 crowd favorite, backed by countless reviews.

Watch the Demo


Read the Blog


Learn More
