Define once. Trust everywhere.
Define business logic one time, in one place, and use it everywhere. Power accurate AI and analytics across your entire stack.
Request a DemoAbout data models
Sigma's data models let teams build tables, metrics, and joins one time, then reuse them anywhere. Centrally manage these governed assets directly on your warehouse to guarantee consistent, accurate analytics across the business.
Trusted by 2,000+ leading enterprises around the world
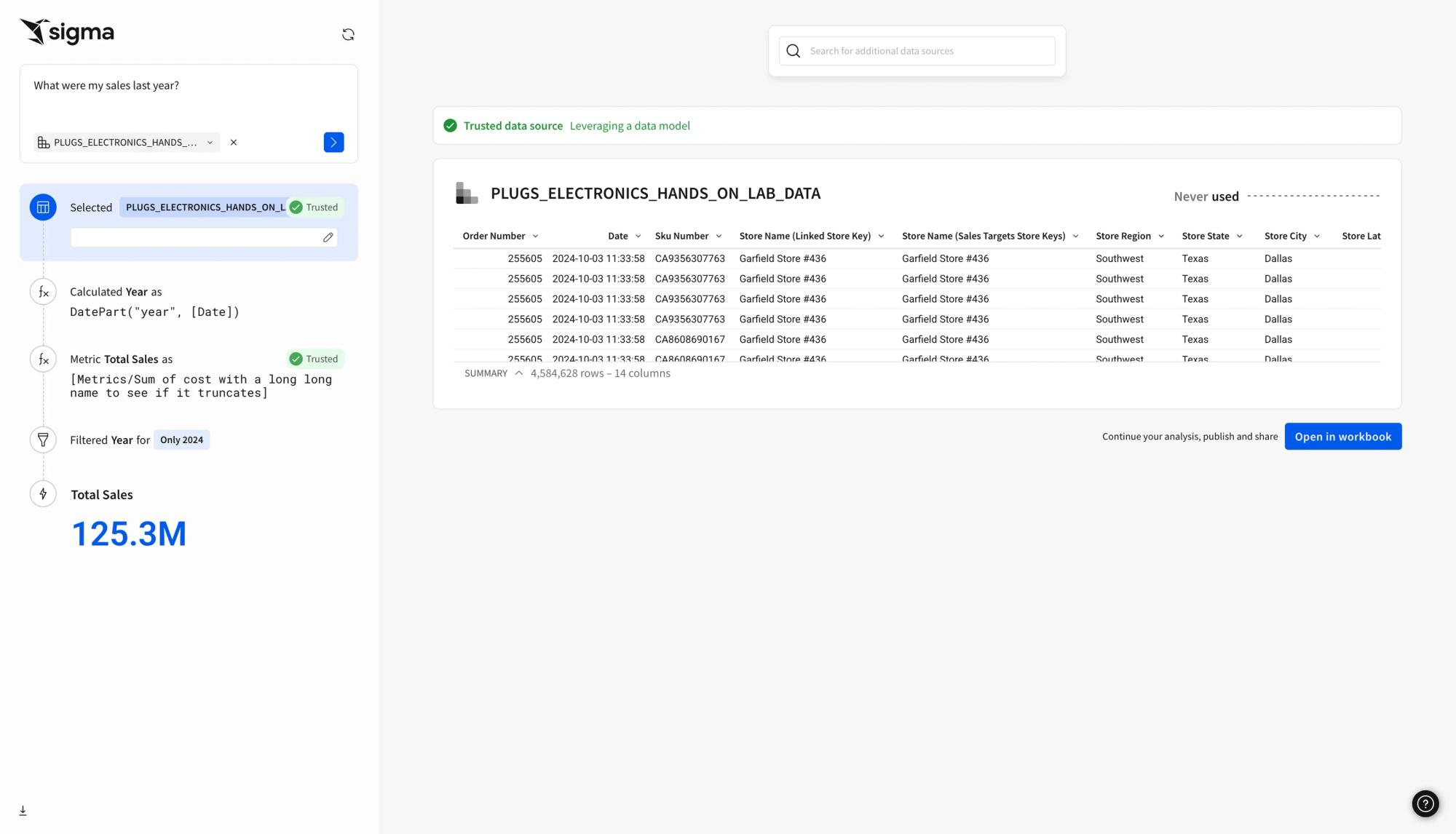
AI-ready context
Ensure AI-generated queries stay accurate and aligned with your organization’s definitions by grounding AI outputs in governed semantic context.
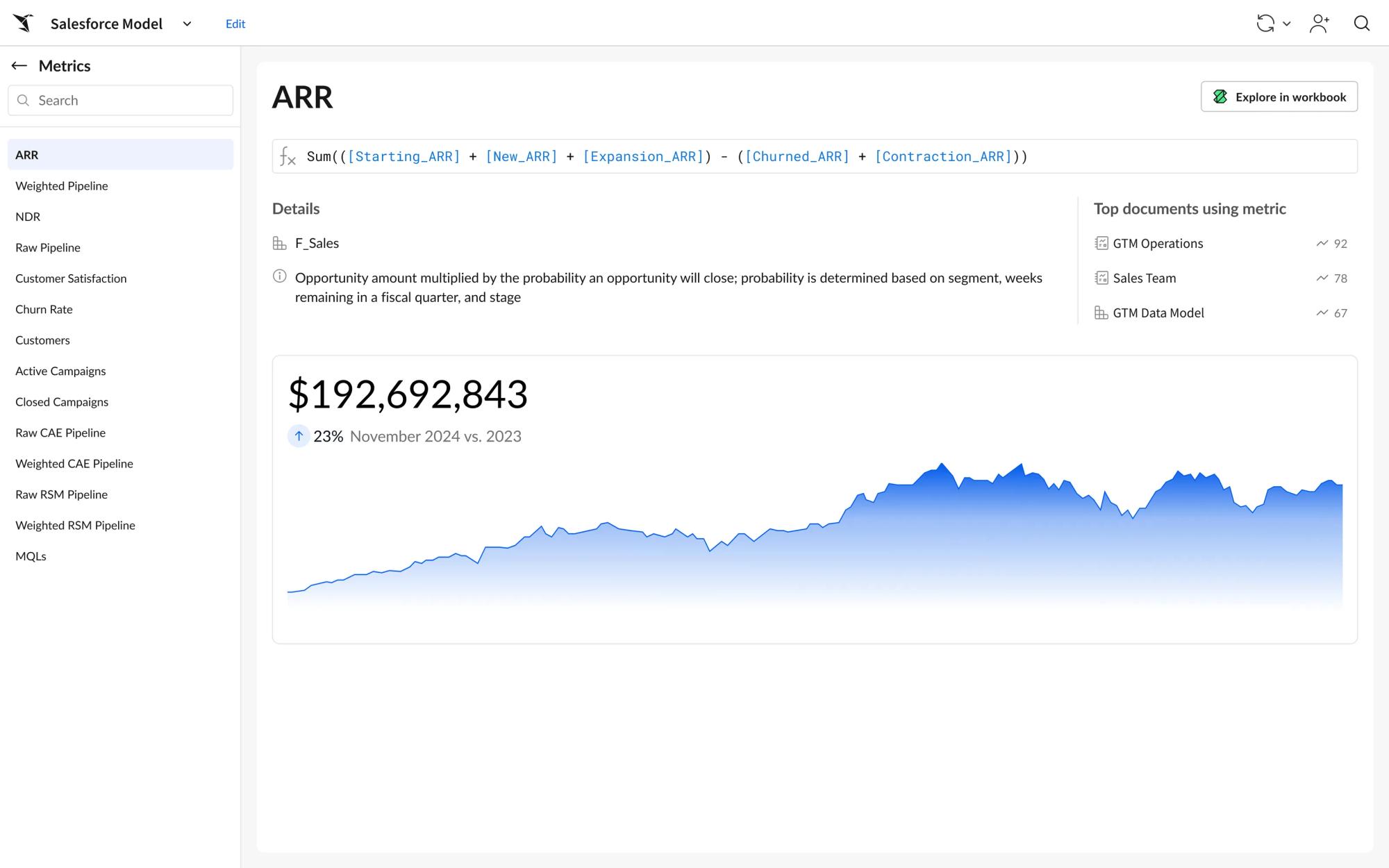
Governed metrics at scale
Centrally define metrics, relationships, and business logic so every analysis uses consistent definitions for trusted insights at scale.
Integrated into your ecosystem
Built natively on your cloud data warehouse. Use your data model or our semantic layer with to define trusted metrics and business logic.
Intelligent data modeling
The foundation for governed, scalable analytics—backed by code.
Unified metrics and business logic
Create reusable business definitions that serve both your end users and your AI agents. Ensure your entire organization uses the same definitions, from revenue to active customers.
- AI-ready: Give richer context to LLMs without requiring users to work directly in the warehouse.
- Consistent: Leverage the same trusted metrics across all your tools.
- Integrated: Deliver accurate insights across your stack—using your data model or our semantic layer.
Give AI the context it needs
Define and govern semantics once so your AI delivers accurate insights. Curate warehouse metadata, semantic layers, and usage signals to ensure AI understands your business logic, not just the raw data.
- Governed logic: Centralized definitions ensure consistent metrics everywhere.
- AI-ready context: Curate data, semantic layers, and behavior to ground AI answers.
- Trusted answers: Reliable, accurate AI outputs aligned with your business meaning.
Code-first data models
Define and manage reusable data models entirely in code. Build, version, and automate models that power consistent analytics and collaborative workflows across your organization.
- Code-first: Create, update, and maintain models using YAML, with full version control and CI/CD workflow compatibility.
- Reusable: Publish tables, metrics, joins, and relationships once and consume them across workbooks, dashboards, and AI workflows.
- Governed: Enforce RBAC, approvals, and modular model design to ensure consistency and maintainable business logic across your data ecosystem.
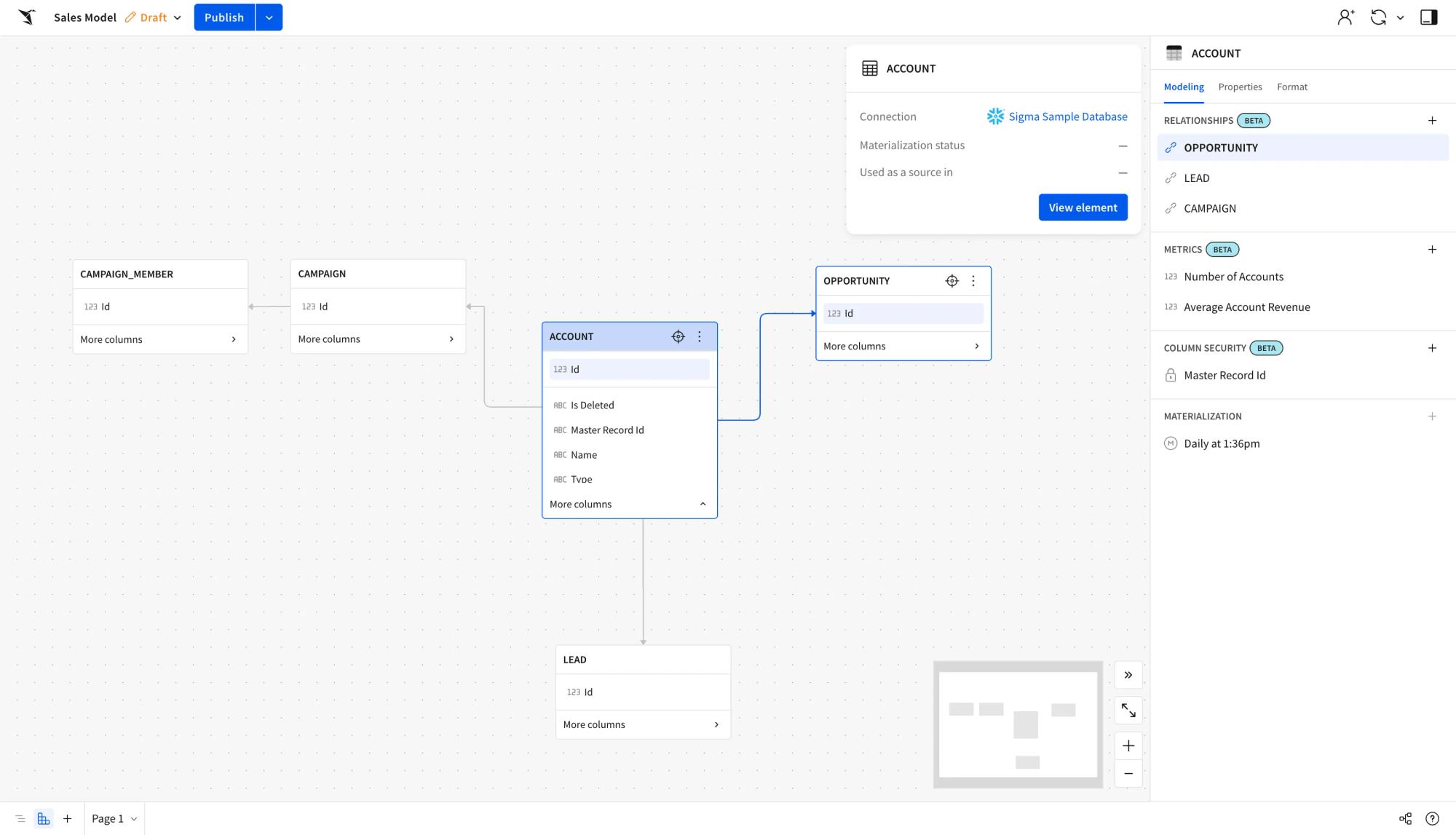
Centralized management of your data
Modular governance with RBAC and approvals ensures scalable, secure, and reusable data assets. Roles and RLS are inherited directly from your warehouse for safe, efficient analysis.
- Version tagging: Manage multiple data model versions for easier iteration and development.
- Column level security: Restrict sensitive data to authorized users only.No external caches:
- Warehouse-native caching reduces query times without exposing data.

Enterprise-ready semantics
From raw warehouse tables to trusted business insights. See how customers build scalable data foundations with Sigma.

 Customer Story
Customer Story“We’re working toward ensuring there’s a data model for every pod. That way, teams can self-serve answers through a consistent structure.”
Related Resources

How to Curate the Right Context for AI Agents
Learn how to curate the right context for AI agents, combining data, semantic layers, and human behavior to ensure accurate, reliable, and enterprise-ready AI outputs.

Building Governed Data Models With Sigma
Download the whitepaper to learn how Sigma Data Models bring governed data modeling, trusted metrics, and agility to your cloud warehouse.

How To Build Governed Self-Service That Actually Scales
Empower business users and data teams with governed, AI-ready analytics using Sigma’s flexible, reusable data models. Scale insights without the overhead.










